AWS WAF Obfuscation: Patterns and Techniques
Overview of manual and automated AWS WAF obfuscation methods, their effectiveness, scalability, and cost trade-offs including token solving and TLS spoofing.

AWS WAF obfuscation involves disguising malicious payloads (like SQL injection or XSS attacks) to bypass detection. Attackers exploit how AWS WAF and backend systems process requests differently, using methods like encoding, JSON key duplication, or payload padding. These techniques aim to evade rules while remaining executable by target web applications.
Key points:
- Manual Methods: Includes JSON key duplication (e.g.,
{"id": 1, "id": "attack"}), Unicode escape sequences, and exceeding AWS WAF's inspection limits (8 KB for ALB, 64 KB for CloudFront). Effective but labor-intensive and hard to scale. - Automated Solutions (e.g., PeakFO): Tools like PeakFO automate bypasses using token solving, TLS fingerprint impersonation, and intelligent fallback mechanisms. They offer faster, scalable solutions with success rates above 99%.
Comparison:
- Manual methods are suitable for small-scale tests but require deep technical knowledge and significant effort.
- Automated tools like PeakFO are faster, scalable, and cost-effective for high-demand operations.
For organizations, balancing manual and automated strategies is critical to address evolving threats.
#NahamCon2024: The Art of Bypassing WAFs (with live demos!) | @Brumens2
1. Manual AWS WAF Obfuscation Methods
When looking at manual obfuscation techniques, it becomes clear how attackers exploit the differences in how AWS WAF and backend systems process data. These methods often involve tactics like JSON key duplication, Unicode escape sequences, and payload padding (adding extra data to bypass size limits), all designed to sneak malicious code past detection rules.
One common technique is JSON key duplication, where attackers send payloads like {"id": 1, "id": "attack"}. AWS WAF might only analyze the first key, while backend systems like PHP or Python use a "last-value-wins" approach, executing the second key instead. Another method involves Unicode escape sequences in JSON keys. For instance, attackers might use \u0069 instead of "i" to disguise parameter names.
"AWS WAF, in its current implementation, does not decode escape sequences inside JSON keys when matching a given JSON Pointer of a rule"
- Andrea Menin, Sicuranext
Attackers also rely on payload padding to bypass AWS WAF's inspection limits, which are 8 KB for Application Load Balancers and up to 64 KB for CloudFront.
Effectiveness
Manual obfuscation methods are particularly effective at exploiting specific WAF weaknesses. For example, in January 2024, the Sysdig Threat Research Team discovered that the experimental onbeforetoggle DOM event could bypass AWS Managed Rules entirely. This highlighted how experimental HTML5 events can evade static signature-based detection. Although AWS patched this vulnerability on December 13, 2023, the incident exposed ongoing detection gaps. Additionally, research shows that over 90% of websites accept both application/x-www-form-urlencoded and multipart/form-data formats, providing attackers with more opportunities to exploit. However, while effective, these techniques often face scalability challenges.
Scalability
Scaling manual obfuscation techniques is a significant hurdle.
"Due to the vast amount of tags and events, it turned out to be almost impossible to test every single permutation and combination of payloads to find edge cases not covered by the WAF"
- Sysdig Threat Research Team
Attackers need to customize payloads for each specific environment, and every WAF update requires fresh testing. This constant tweaking creates a heavy maintenance burden for both attackers and defenders. For defenders, managing signature-based rules is resource-intensive, as they must update rules to counter new obfuscation techniques. This can lead to bloated rule databases that consume significant Web ACL Capacity Units (WCUs).
Cost Efficiency
Manual obfuscation drives up costs for both sides. For defenders, AWS WAF applies text transformations like URL_DECODE or JS_DECODE, each consuming 10 WCUs. More complex detection rules, such as those for SQL injection (20 WCUs) or cross-site scripting (40 WCUs), significantly increase operational expenses. Inspecting JSON bodies doubles the base WCU cost of match statements. Exceeding the 1,500 WCU threshold results in extra charges beyond the base protection pricing. For attackers, the time and effort required for manual testing are substantial, and success is never guaranteed, especially as WAF vendors actively patch known vulnerabilities.
Ease of Integration
Implementing manual obfuscation requires a deep understanding of both WAF rules and backend parsing behavior. Attackers need to know how various frameworks handle malformed data. For instance, whether a Node.js application uses Busboy or Formidable for multipart parsing can make a difference, as each has unique vulnerabilities. Defenders face similar challenges. AWS WAF's default "None" handler for invalid JSON allows malicious requests to go uninspected. To counter this, security teams must configure multiple text transformations, enforce strict oversize handling policies, and validate JSON at the application level. This steep learning curve often leads to misconfigurations, leaving systems exposed even with WAF protection in place. These complexities highlight the importance of carefully designed WAF configurations to address obfuscation techniques effectively.
2. PeakFO AWS WAF Packages
Unlike manual obfuscation methods, PeakFO provides an automated solution that addresses scalability and integration challenges effectively.
PeakFO streamlines AWS WAF bypass by solving cryptographic tokens. It extracts encrypted parameters like key, iv, and context from the window.gokuProps object and computes the token locally in less than 100 milliseconds. This is significantly faster compared to browser-based automation, which typically takes 5–10 seconds per token.
The platform also uses TLS fingerprint impersonation, leveraging tools like curl-impersonate to replicate browser handshake signatures, cipher suites, and HTTP/2 settings for browsers such as Chrome or Firefox. PeakFO's Combined Bypass Engine focuses on the fastest methods first, such as TLS spoofing, and only resorts to more complex techniques - like token solving or stealth-patched browser automation - when necessary. Additionally, it can exploit AWS WAF's 8KB body inspection limit by padding POST request bodies beyond this threshold.
Effectiveness
PeakFO combines multiple evasion techniques to achieve a success rate exceeding 99%. Cryptographic token solving handles AWS WAF challenges, while TLS fingerprint spoofing avoids detection. This layered approach ensures that if one method fails, others are ready to step in, maintaining efficiency and reliability.
Scalability
This solution is designed to handle unlimited scalability, with no restrictions on concurrent requests or traffic volume. Since token generation relies on local computation rather than browser automation, it can manage high traffic loads without slowing down. The API-based integration allows horizontal scaling, ensuring that developers can expand their applications without encountering WAF challenge bottlenecks. It’s worth noting that PeakFO's AWS WAF solutions are optimized for iOS and Android SDK CAPTCHA challenges, not web-based ones. This specialization simplifies integration and reduces costs.
Cost Efficiency
PeakFO’s pricing model adds to its appeal by charging only for successful solves. Failed attempts, timeouts, and proxy errors incur no charges. The standard rate is $0.80 per 1,000 solves, but bulk packages can lower costs to $0.40 per 1,000, offering discounts of up to 50%. Pay-per-solve balances never expire, making this option ideal for testing, while higher-volume packages are valid for 30 days. In comparison, AWS WAF's native CAPTCHA pricing charges $0.40 per 1,000 attempts regardless of success.
| Package Size | Price | Rate per 1,000 Solves | Discount |
|---|---|---|---|
| Pay Per Solve | Variable | $0.80 | 0% |
| 50K Solves | $30.00 | $0.60 | 25% |
| 100K Solves | $55.00 | $0.55 | 31% |
| 500K Solves | $225.00 | $0.45 | 44% |
| 1M Solves | $400.00 | $0.40 | 50% |
Ease of Integration
PeakFO simplifies integration with dedicated API keys, account management through a Telegram bot, and support for multiple cryptocurrencies like BTC, LTC, ETH, USDT (TRC20/ERC20), and TON. Developers can monitor usage via the /getbalance endpoint, making it easy to track and plan for refills. This streamlined process eliminates the need for deep expertise in WAF rules, allowing developers to implement AWS WAF bypass capabilities with just a few lines of code.
Pros and Cons
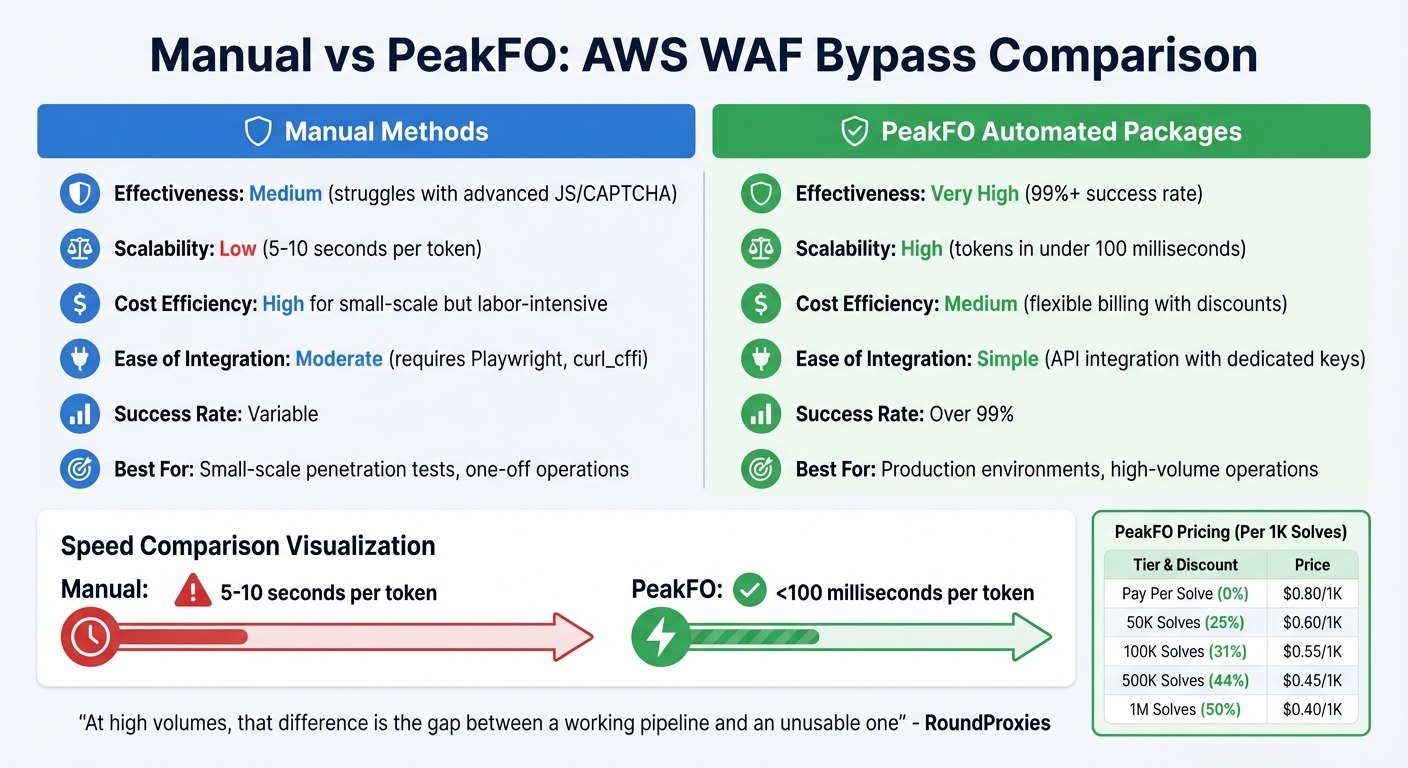
Manual vs Automated AWS WAF Obfuscation: Performance and Cost Comparison
Manual obfuscation methods give you full control without the need for software fees, making them an appealing choice for one-off penetration tests or smaller operations. Techniques like TLS fingerprint spoofing with curl_cffi or padding POST bodies beyond the 8 KB inspection limit can be effective against low-to-medium sensitivity WAF configurations. However, these methods come with limitations. For instance, using Playwright for token generation can take 5–10 seconds per token, which creates a bottleneck for high-volume tasks. Additionally, maintaining these methods can be a headache due to frequent WAF updates.
"A Playwright instance takes 5–10 seconds per token. The solver generates one in under 100 milliseconds. At high volumes, that difference is the gap between a working pipeline and an unusable one" - RoundProxies
On the other hand, PeakFO's automated system eliminates these delays with a streamlined approach. By leveraging cryptographic token solving, TLS fingerprint impersonation, and intelligent fallback mechanisms, PeakFO achieves a success rate of over 99%. The service also offers flexible billing options, including pay-per-solve and bulk discounts, ensuring you only pay for successful attempts.
Here’s a quick comparison of manual methods versus PeakFO packages:
| Criteria | Manual Methods | PeakFO Packages |
|---|---|---|
| Effectiveness | Medium; struggles with advanced JS/CAPTCHA | Very High; over 99% success rate |
| Scalability | Low; 5–10 seconds per token | High; tokens generated in under 100 ms |
| Cost Efficiency | High for small-scale but labor-intensive | Medium; flexible billing with discounts |
| Ease of Integration | Moderate (e.g., Playwright, curl_cffi) |
Simple API integration with dedicated keys |
Manual methods shine in specific scenarios, such as exploiting unique parsing quirks - like tweaking multipart/form-data boundaries or using experimental DOM events like onbeforetoggle, which automated tools might not yet handle. However, for production environments that demand unlimited concurrent requests and consistent sub-second performance, PeakFO’s automated tools are the better option.
"Organizations should never solely rely on out-of-the-box solutions and must constantly adapt and test their security controls to stay ahead of evolving threats" - Daniele Linguaglossa, Sysdig Threat Research Team
Ultimately, choosing the right method depends on understanding AWS WAF's rule patterns and how evolving obfuscation techniques influence detection mechanisms.
Conclusion
Choose your obfuscation strategy based on the specific needs of your project and its scale. Manual techniques are ideal for smaller penetration tests where precision and granular control are essential. These methods take advantage of subtle parsing quirks, potentially bypassing certain AWS WAF rules effectively.
On the other hand, manual methods can quickly become impractical for larger-scale operations or environments requiring continuous monitoring. For example, manual browser automation can take 5–10 seconds per token, whereas PeakFO's system can generate tokens in under 100 milliseconds. With success rates exceeding 99% and the ability to handle unlimited concurrent requests, PeakFO ensures dependable performance for businesses that demand speed and reliability.
"Organizations should never solely rely on out-of-the-box solutions and must constantly adapt and test their security controls to stay ahead of evolving threats." - Daniele Linguaglossa, Sysdig Threat Research Team
The main takeaway? Security measures must constantly adapt to keep up with evolving threats. While manual methods are cost-effective and provide flexibility for controlled testing, businesses that rely on efficient AWS WAF challenge-solving - whether for competitive analysis, price tracking, or large-scale data aggregation - benefit from PeakFO’s automated solution. With structured pricing and enterprise-level reliability, it eliminates the operational burden of manual efforts.
Manual techniques are great for understanding obfuscation mechanics, but PeakFO's automation is the go-to choice for scalable and consistent results. Your decision ultimately depends on whether you’re experimenting with the basics or running a high-demand operation that requires dependable performance.
FAQs
How can I tell if AWS WAF is parsing a request differently than my backend?
To determine if AWS WAF processes a request differently from your backend, take a close look at the WAF's text transformations and request component settings. These configurations can modify data before it reaches your backend, potentially leading to differences in how requests are handled. By comparing these settings with your backend's request processing, you can pinpoint any inconsistencies in parsing behavior.
How can I prevent JSON key-duplication and Unicode-escape bypasses?
To avoid issues like JSON key duplication and Unicode-escape bypasses in AWS WAF, you can take several steps to strengthen your defenses. Start by enabling JSON inspection to identify duplicate keys effectively. Then, configure precise match patterns to ensure your filters catch the intended data.
Next, use text transformations, such as decoding, to normalize the content. This step helps prevent attackers from exploiting Unicode escape sequences to bypass your rules.
Finally, set the InvalidFallbackBehavior parameter to either block or alert when invalid JSON is detected. This ensures that malformed JSON structures can't be used as a loophole to exploit your system.
How do AWS WAF body inspection limits affect real-world protection?
AWS WAF has limits on the size of request components it can inspect. For instance, the inspection limit is 8 KB for services like Application Load Balancer and AWS AppSync. For CloudFront and API Gateway, the default limit is 16 KB, but this can be increased to 64 KB if needed. Any request body exceeding these limits will be truncated, meaning only the portion within the limit is analyzed. This truncation may leave the system less effective against attacks that use larger payloads.