How Proxies Circumvent AWS WAF Rules
Proxies hide attacks by masking IPs, manipulating headers, rotating addresses, and exploiting inspection limits—forcing active, adaptive defenses.
AWS WAF protects web applications from threats like SQL injection, XSS, and bots. But attackers often bypass these defenses using proxies. Proxies mask the true IP, manipulate headers, and rotate addresses to evade rules. They also exploit AWS WAF's inspection limits (e.g., 8KB request body cap) and rate-limiting mechanisms.
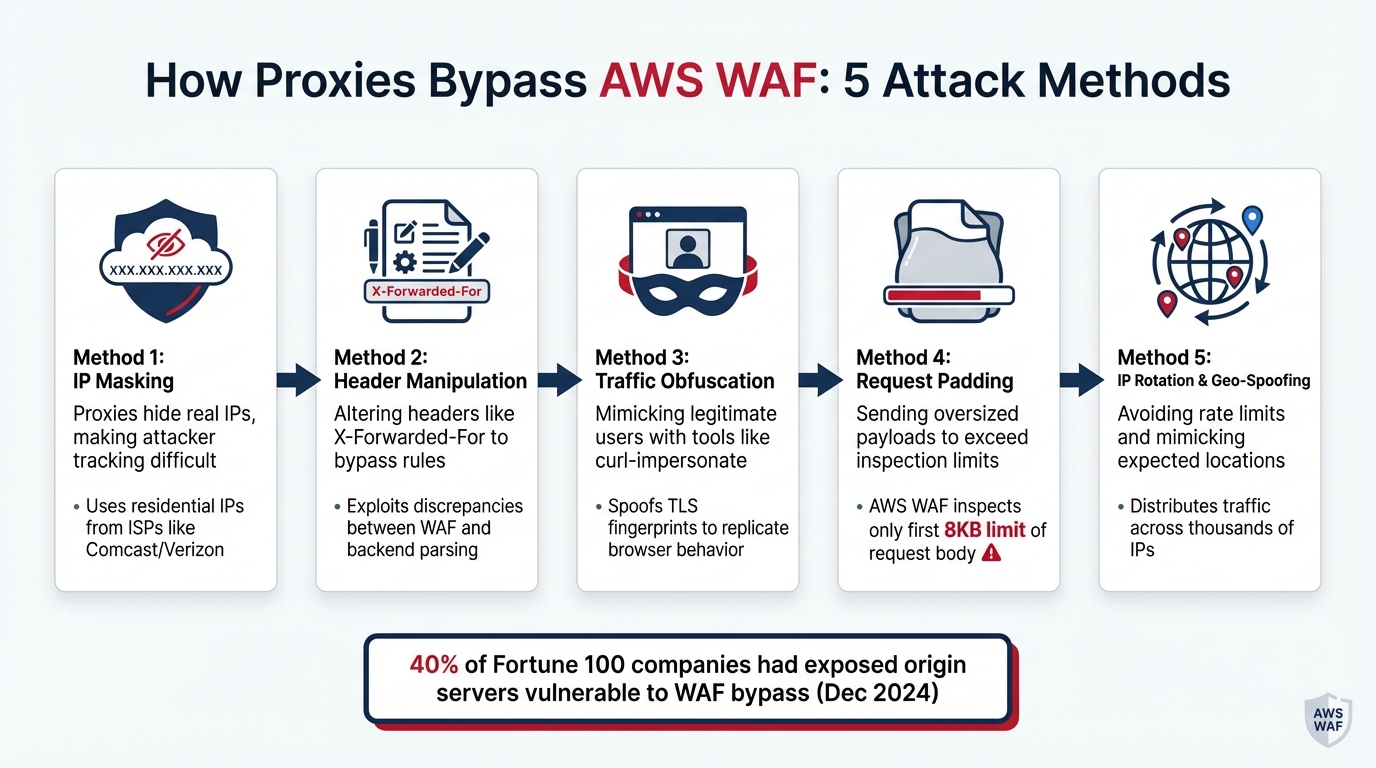
Key Methods Attackers Use:
- IP Masking: Proxies hide real IPs, making it hard to track attackers.
- Header Manipulation: Altering headers (e.g.,
X-Forwarded-For) to bypass rules. - Traffic Obfuscation: Mimicking legitimate users with tools like
curl-impersonate. - Request Padding: Sending oversized payloads to exceed inspection limits.
- IP Rotation & Geo-Spoofing: Avoiding rate limits and mimicking expected locations.
Defensive Measures:
- Use machine learning for traffic analysis.
- Employ rate-limiting rules and CAPTCHA challenges.
- Regularly update WAF rules and analyze traffic logs.
- Leverage AWS WAF's managed rules and Traffic Insights.
Proxies exploit AWS WAF's limitations, but combining advanced configurations, machine learning, and regular updates can reduce their effectiveness.
5 Key Methods Attackers Use to Bypass AWS WAF with Proxies
Modern WAF Bypass Scripting Techniques for Autonomous Attacks
How Proxies Evade AWS WAF Rules
Proxies use specific strategies to sidestep AWS WAF rules, taking advantage of how the firewall processes and analyzes traffic. These techniques highlight the limitations of traditional rule-based security when dealing with advanced attackers.
Traffic Obfuscation Methods
One of the most common methods attackers use is disguising malicious traffic to make it appear like legitimate browser activity. For instance, tools like curl-impersonate allow proxies to mimic browser TLS fingerprints, preventing AWS WAF from flagging automated scripts based on their network signatures.
Another tactic involves exploiting AWS WAF's inspection limits. Attackers pad POST requests to exceed the default inspection threshold - 8KB for AWS WAF or 64KB for CloudFront and API Gateway - so that harmful content is hidden from the firewall's view .
"AWS WAF only inspects the first 8,192 bytes (8KB) of a request body by default. Anything beyond that limit gets forwarded directly to the origin server without inspection." – RoundProxies Blog
Attackers also evade detection by manipulating patterns using techniques like Unicode obfuscation, alternating character cases (e.g., <sCrIpT>), replacing parentheses with backticks, or embedding comments within SQL statements. These methods make malicious payloads harder for AWS WAF's pattern-matching algorithms to detect.
IP Rotation and Geo-Spoofing
Beyond disguising the content of traffic, proxies also manipulate the origin of requests. By rotating IP addresses, proxies distribute traffic across thousands of unique sources, making it difficult for AWS WAF to enforce rate-limiting rules. Since AWS WAF monitors request volumes from individual IPs over short intervals (e.g., one minute), spreading requests across multiple IPs ensures no single address exceeds the limit .
Proxies also use geo-spoofing to bypass geographic restrictions. AWS WAF can allow or block traffic based on the country of origin, but proxies reroute traffic to match expected user profiles. For example, a request claiming to come from a US-based Chrome browser will also originate from a US IP address to avoid triggering behavioral analysis flags.
In December 2024, Zafran Security's analysis revealed that 40% of Fortune 100 companies had domains with exposed origin servers. This vulnerability allowed attackers to bypass WAF protections entirely by targeting the origin IPs directly, rendering geographic and IP-based restrictions ineffective.
Header Manipulation and Payload Encoding
Attackers also exploit weaknesses in AWS WAF's handling of headers and payloads to evade detection.
For example, proxies can manipulate headers by altering fields like Content-Length to obscure critical information from the WAF while ensuring it reaches the backend server intact. A notable case in 2021 involved a researcher bypassing AWS API Gateway IP restrictions by appending characters to the X-Forwarded-For header. While the frontend server ignored the mutated header, the backend parsed it as a trusted IP source.
Another common trick involves exploiting discrepancies in how AWS WAF and backend systems interpret complex content types. In multipart/form-data requests, attackers can include a fake boundary for AWS WAF to inspect while hiding the actual payload behind a real boundary processed only by the backend. A 2021 study found that over 90% of websites accepted both application/x-www-form-urlencoded and multipart/form-data formats interchangeably, making this tactic widely applicable.
AWS WAF has its limits when inspecting headers, only analyzing up to 200 headers or 8,192 bytes. Attackers take advantage of this by using encoding techniques like Base64, CSS escapes, or HTML entities to hide malicious content within these constraints. While AWS WAF can apply text transformations to decode such content, complex or layered obfuscation may still slip through if the firewall isn't configured to apply the correct transformation sequence.
Why Proxy-Based Evasion Is Hard to Detect
Even with well-crafted rules, detecting proxy-based evasion remains a tough challenge.
Constantly Changing Proxy Traffic
One of the biggest hurdles is how advanced proxies mimic legitimate traffic. These proxies route their requests through residential IPs provided by ISPs like Comcast or Verizon, making their activity nearly identical to that of real users. While AWS WAF maintains reputation lists for datacenter IP ranges (e.g., AWS, GCP, Hetzner), residential IPs easily bypass these initial defenses.
Proxies also rely on constant IP rotation to stay under the radar. AWS WAF, for example, monitors request volumes from individual IPs over short intervals (e.g., one minute). By spreading requests across thousands of IPs, proxies ensure each address stays below rate-limiting thresholds. Even when AWS WAF issues token challenges that remain valid for 5–15 minutes, attackers can solve the challenge once and reuse the token across multiple proxy IPs.
Adding to the complexity, proxies use techniques like "jitter" - randomized delays between requests - to mimic human browsing speeds. They also spoof TLS fingerprints to replicate genuine browser behavior. These tactics make proxy traffic virtually indistinguishable from real user activity. By evading rate-based detection, attackers create opportunities to exploit more advanced bypass techniques, such as structural mutations.
Limitations of Rule-Based Detection
Proxies don't just rely on dynamic IP rotations - they also exploit the inherent weaknesses of static rule-based detection. Traditional AWS WAF rules depend on regex-based pattern matching to identify known attack signatures. However, attackers often outpace updates to these static rules, leaving gaps in detection.
In January 2024, Daniele Linguaglossa from the Sysdig Threat Research Team highlighted this issue. He demonstrated how the experimental onbeforetoggle DOM event could execute JavaScript while bypassing AWS WAF's managed rules. Using a specialized fuzzer, his team crafted a payload that linked a standard HTML button to a popover element - something AWS WAF’s regex-based detection missed entirely. AWS acknowledged this vulnerability in October 2023 and rolled out a fix in December 2023.
The WAFFLED research project further exposed the limitations of static rules. Researchers identified 1,207 confirmed bypasses across five major WAFs, including AWS. They also found that over 90% of websites accepted both application/x-www-form-urlencoded and multipart/form-data content types interchangeably, enabling attackers to manipulate content types for evasion.
"If the WAF sees one thing and the server sees another, you've found your bypass." – Penetration Tester's Handbook
Attackers have also shifted from focusing solely on payloads to targeting HTTP structures themselves. By altering headers, boundaries, and body segments, they can confuse WAF parsers while ensuring backend servers still process the intended code. This evolution from payload-based to structure-based evasion makes traditional signature-matching approaches far less effective.
How to Reduce Proxy-Based Evasion in AWS WAF
AWS WAF provides several tools and strategies to help mitigate proxy-based evasion. While it's nearly impossible to eliminate this threat entirely, combining these techniques can make it significantly less effective.
Using Machine Learning Models
AWS WAF employs machine learning to analyze request patterns and browser characteristics, helping to differentiate proxy traffic from legitimate users. One useful method is volumetric baselining, where the system compares current session activity to historical traffic patterns. For example, rules like TGT_VolumetricSession can detect unusual spikes often linked to proxy-based automation. Additionally, device fingerprinting collects details such as CPU, memory, and OS version to identify repeated requests from the same physical device, even when bots use rotating proxies.
It’s important to note that machine learning rules require a 24- to 72-hour warm-up period to become effective. To maximize protection, enable targeted Bot Control during periods of normal traffic. You can also integrate AWS WAF’s JavaScript and mobile SDKs for better session tracking. These machine learning techniques work best when paired with other defenses like rate limiting and CAPTCHA challenges.
Implementing Rate Limiting and CAPTCHA Challenges
Rate limiting is a practical way to counter proxy-based evasion. Instead of focusing solely on the immediate source IP, configure rate-based rules to aggregate by FORWARDED_IP, which identifies the original client.
A smart approach is to use dual rate-based rules: one with a high threshold to block malicious activity and another with a low threshold for silent CAPTCHA challenges. The silent CAPTCHA action performs browser verification behind the scenes, avoiding the frustration of traditional CAPTCHA puzzles. For APIs, you can adjust the "Immunity Time" so that valid challenge tokens persist across multiple requests.
Before deploying these rules, test them in "Count" mode to gauge their impact on legitimate traffic. Additionally, when inspecting forwarded IP headers, set the fallback behavior to "MATCH" for requests with missing or malformed headers. This prevents attackers from bypassing rules by stripping these headers.
For handling a large volume of CAPTCHA challenges, services like PeakFO (https://peak.fo) can programmatically solve AWS WAF challenges with fast response times and pricing plans starting at $30 for bulk packages.
To stay effective, these defenses need to be regularly updated, as explained in the next section.
Keeping WAF Rules Updated
Regularly updating WAF rules is essential to counter evolving proxy evasion tactics. AWS Managed Rules automatically update to include the latest malicious IPs and bot signatures. These rules come in two options: "Default" versions that update automatically and "Static" versions for controlled testing.
AWS also provides a Managed Rules changelog that lists new detection signatures and updates. For instance, Bot Control Version 4.0 introduced Web Bot Authentication (WBA), which uses cryptographic verification for AI bots and agents. Reviewing this changelog can help you understand new protections and refine your rules.
The AWS WAF dashboard offers Traffic Insight Recommendations, analyzing up to two weeks of allowed traffic to identify potential gaps in your defenses. When implementing these recommendations, use scope-down statements to focus intelligent threat mitigation rules on the most relevant traffic. Position basic, cost-effective rules (like IP blocking) ahead of higher-cost mitigation rules to filter out obvious threats early.
Lastly, keep in mind that updates to web ACLs, rule groups, or IP sets may take a few seconds to several minutes to propagate globally. Plan these updates during low-traffic periods and monitor metrics closely after deployment.
Conclusion
Summary of Proxy Evasion Methods
Attackers have developed several ways to bypass AWS WAF rules. Techniques include padding request bodies, rotating residential IPs, and spoofing TLS fingerprints using tools like curl_cffi to mimic real browser behavior. Some advanced methods exploit differences in how WAFs and backend servers parse requests, allowing harmful payloads to slip through undetected. Additionally, attackers rely on header smuggling and solving JavaScript challenges to reverse-engineer the aws-waf-token, enabling automated access without triggering alarms. These strategies highlight the importance of continuously fine-tuning WAF configurations.
Why Active WAF Management Matters
Default WAF settings often fall short against sophisticated threats. As attackers evolve their techniques, active management becomes a necessity. Daniele Linguaglossa from the Sysdig Threat Research Team advises, "Organizations should never solely rely on out-of-the-box solutions and must constantly adapt and test their security controls to stay ahead of evolving threats". A study of Fortune 1,000 companies revealed that nearly 20% were vulnerable to WAF bypass due to exposed origin server IPs, and only 13% had properly implemented mTLS to block direct access. To address these vulnerabilities, organizations should focus on regular testing in staging environments, monitoring logs meticulously, and updating rules based on live traffic patterns. Even advanced managed rules require this level of attention to remain effective.
The Future of WAF Security
The future of WAF security lies in adaptive, AI-powered defenses. Tools are already moving toward machine learning and behavioral analysis to counter increasingly complex attacks. For instance, AWS WAF now offers Traffic Insight Recommendations, which analyze two weeks of traffic data to suggest optimizations tailored to specific applications. Emerging solutions like HTTP-Normalizers aim to resolve parsing inconsistencies by validating requests against RFC standards before they reach the WAF. As attackers refine their methods, integrating AI-driven detection, proactive fuzzing, and architectural measures like mTLS will be critical for ensuring strong WAF protection. For handling high-volume CAPTCHA challenges, using fast-solving APIs like PeakFO can also provide an edge.
FAQs
How can I stop attackers from hitting my origin server directly?
To keep your origin server safe, set up AWS WAF rules to block direct access. Use rate-based rules with IP aggregation to control the number of requests coming from individual IPs. Also, make sure to inspect forwarded IP addresses so that only traffic from authorized proxies or load balancers gets through to your server. Pair these steps with strict web ACLs to filter out untrusted requests and strengthen your defense against direct attacks.
Which AWS WAF settings best reduce proxy IP rotation evasion?
To tackle proxy IP rotation evasion, set up rate-based rules with detailed scope-down statements. By leveraging forwarded IP addresses - such as those in the X-Forwarded-For header - you can more precisely monitor and control request rates from the original clients. This approach allows you to pinpoint and manage high-frequency requests more effectively.
How do I tune AWS WAF body inspection limits safely?
To make adjustments to AWS WAF body inspection limits safely, it's important to keep the default size limits in mind - 8 KB for Application Load Balancer (ALB) and 16 KB for CloudFront. These limits determine how much of the request body AWS WAF can inspect.
For handling requests that exceed these size limits, you can use the OversizeHandling setting. This setting lets you decide how AWS WAF should respond to oversized requests by choosing one of the following actions:
CONTINUE: Proceed with inspection of the available portion of the body.MATCH: Treat the oversized request as a match for the rule.NO_MATCH: Exclude the oversized request from matching the rule.
To avoid security gaps, make sure the inspection limits align with the typical sizes of incoming requests. This reduces the risk of attackers exploiting oversized requests to bypass detection. Regularly monitor your traffic patterns and adjust your rules as needed to stay ahead of potential threats.